Cybersecurity is the practice of protecting digital systems, networks, and data from unauthorized access, attacks, or damage. As technology becomes more integrated into everyday life, cybersecurity plays a vital role in keeping information secure.
From personal devices to large enterprise networks, cybersecurity ensures safe digital operations and protects sensitive data from cybercriminals.
Why Cybersecurity Matters
Cybersecurity is essential in today’s digital world, where personal, financial, and business data are constantly at risk. As cyber threats grow more advanced, strong security measures are critical to protect information and maintain trust.
Protects Sensitive Data
Cybersecurity safeguards personal information such as passwords, banking details, and confidential business data from unauthorized access.
Prevents Financial Loss
Cyberattacks like fraud and ransomware can cause significant financial damage. Effective security measures help reduce these risks.
Ensures Privacy
Strong cybersecurity protects user privacy by preventing unauthorized surveillance and data breaches.
Supports Business Continuity
Organizations rely on secure systems to operate smoothly. Cybersecurity helps prevent downtime caused by attacks such as Distributed Denial-of-Service (DDoS).
Builds Trust and Reputation
Customers are more likely to trust businesses that prioritize data protection. A strong cybersecurity posture enhances credibility and brand reputation.
Protects Against Evolving Threats
Cyber threats continue to evolve, including malware, phishing, and zero-day exploits. Proactive cybersecurity helps defend against these risks.
Compliance With Regulations
Many industries must follow strict security standards set by organizations like the National Institute of Standards and Technology to ensure data protection and legal compliance.
Cybersecurity is not just a technical requirement—it is a fundamental part of protecting digital life. By investing in strong security practices, individuals and organizations can reduce risks and operate safely in an increasingly connected world.
Types of Cybersecurity
Cybersecurity is a broad field that includes multiple layers of protection. Each type focuses on securing a specific part of digital infrastructure, ensuring comprehensive defense against cyber threats.
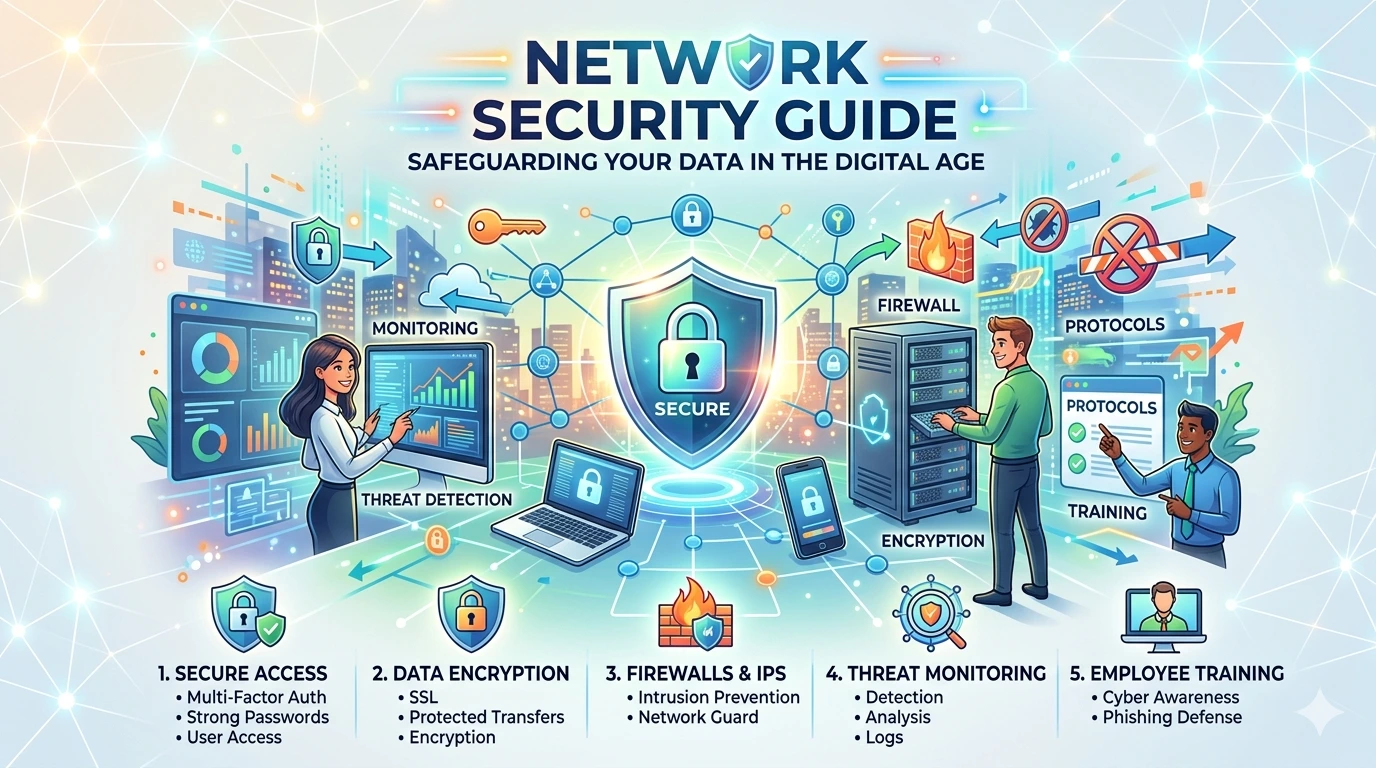
Network Security
Network security protects internal networks from unauthorized access, misuse, or attacks. It includes firewalls, intrusion detection systems, and secure network configurations.
Application Security
Application security focuses on keeping software and applications free from vulnerabilities. This involves secure coding practices, regular updates, and testing to prevent exploitation.
Information Security
Also known as data security, this type ensures the confidentiality, integrity, and availability of information. It protects sensitive data from unauthorized access or alteration.
Endpoint Security
Endpoint security secures devices such as computers, smartphones, and tablets that connect to a network. Tools like Microsoft Defender Antivirus help protect endpoints from threats.
Cloud Security
Cloud security safeguards data, applications, and services stored in cloud environments. It includes encryption, identity management, and monitoring tools.
Identity and Access Management (IAM)
IAM controls who can access systems and data. It uses authentication methods like passwords and multi-factor authentication to ensure only authorized users gain access.
Internet of Things (IoT) Security
IoT security focuses on protecting connected devices such as smart home systems, wearables, and industrial sensors from cyber threats.
Operational Security (OpSec)
Operational security involves processes and decisions that protect sensitive information. It includes policies for data handling, access control, and risk management.
Many organizations follow standards from the International Organization for Standardization to implement structured cybersecurity strategies across these areas.
Understanding these types of cybersecurity helps individuals and organizations build a layered defense system, reducing vulnerabilities and improving overall digital security.
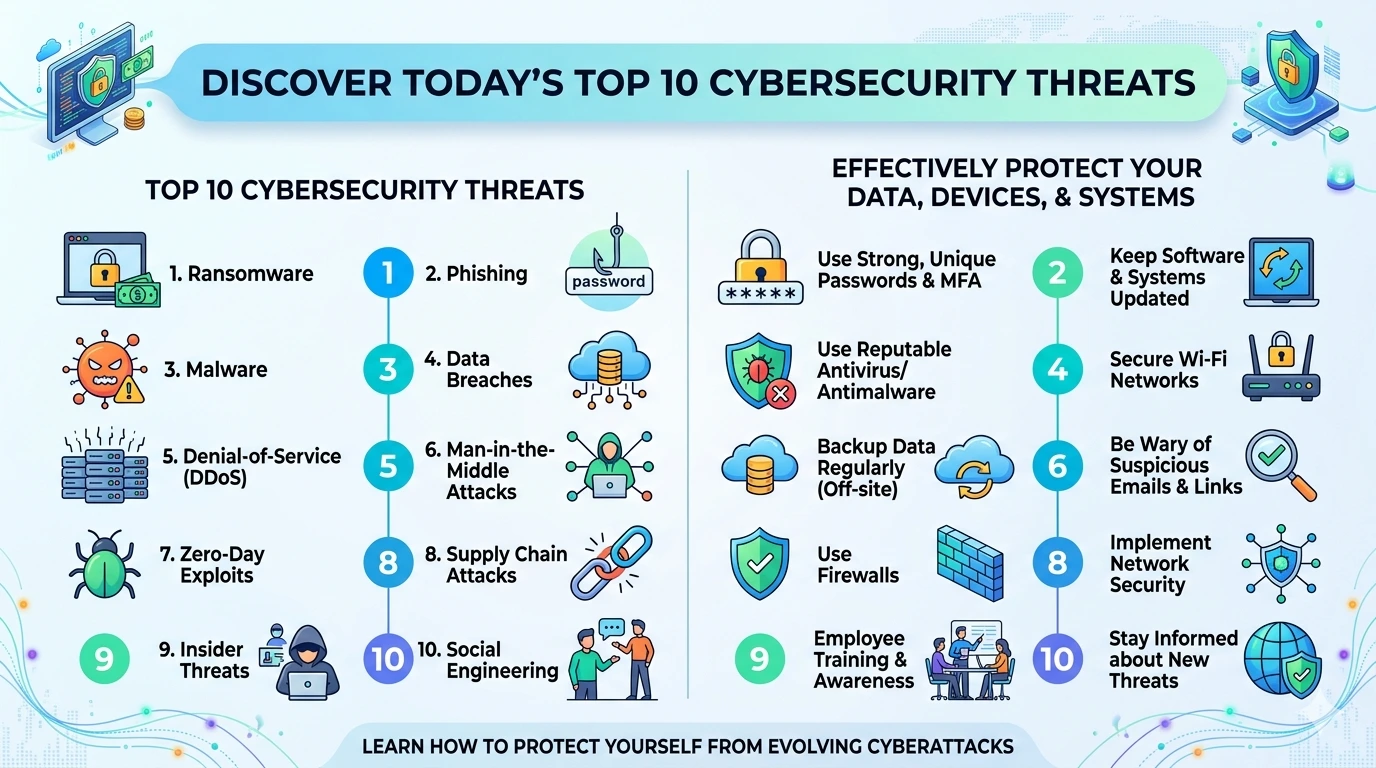
Common Cyber Threats
Cyber threats are constantly evolving, targeting individuals, businesses, and governments. Understanding the most common types of cyberattacks is essential for building effective defenses and staying protected online.
Malware
Malware is malicious software designed to damage, disrupt, or gain unauthorized access to systems. It includes viruses, worms, spyware, and trojans. Once installed, malware can steal data or take control of devices.
Phishing
Phishing attacks use fake emails, messages, or websites to trick users into revealing sensitive information such as passwords or credit card details. These attacks often appear to come from trusted sources.
Ransomware
Ransomware encrypts files or locks systems, demanding payment (usually in cryptocurrency) to restore access. A well-known example is the WannaCry ransomware attack.
Denial-of-Service (DoS) Attacks
DoS attacks flood a system, server, or network with excessive traffic, making it unavailable to legitimate users. A more advanced version is Distributed Denial-of-Service (DDoS), which uses multiple systems.
Man-in-the-Middle (MitM) Attacks
In MitM attacks, cybercriminals intercept communication between two parties to steal or manipulate data without their knowledge.
Social Engineering
This type of attack manipulates human behavior rather than exploiting technical vulnerabilities. Attackers trick users into giving away confidential information or access.
Password Attacks
Cybercriminals use techniques like brute force or credential stuffing to guess or steal passwords and gain unauthorized access to accounts.
Zero-Day Exploits
Zero-day attacks target unknown vulnerabilities in software before developers release a fix, making them particularly dangerous.
Many cybersecurity frameworks, including those from the National Institute of Standards and Technology, recommend a proactive approach to identifying and mitigating these threats.
By understanding these common cyber threats, you can take preventive measures and strengthen your overall cybersecurity posture.
Best Cybersecurity Practices
Adopting strong cybersecurity practices is essential for protecting your data, devices, and online identity. Whether you are an individual user or managing a business, these best practices can significantly reduce your risk of cyberattacks.
Use Strong and Unique Passwords
Create complex passwords that include a mix of letters, numbers, and symbols. Avoid using the same password across multiple accounts, and consider using a password manager.
Enable Multi-Factor Authentication (MFA)
MFA adds an extra layer of security by requiring additional verification, such as a code sent to your phone or generated by an app.
Keep Software and Systems Updated
Regular updates patch security vulnerabilities. Always install updates from trusted sources, such as the Microsoft Security Update Guide.
Use Trusted Security Software
Install reliable antivirus and anti-malware tools like Microsoft Defender Antivirus to detect and block threats in real time.
Be Cautious with Emails and Links
Avoid clicking on suspicious links or downloading attachments from unknown senders. Phishing attacks often disguise themselves as legitimate communications.
Secure Your Network
Use strong Wi-Fi passwords and enable encryption (WPA3 if available). Avoid using public Wi-Fi for sensitive activities unless you use a VPN.
Regularly Back Up Your Data
Keep backups of important files in secure locations, such as external drives or cloud storage. This ensures you can recover data in case of ransomware or hardware failure.
Limit User Access
Only grant access to systems and data when necessary. This reduces the risk of internal threats and accidental data exposure.
Educate and Train Users
Human error is a major cause of security breaches. Regular awareness training helps users recognize and avoid threats.
Monitor and Review Activity
Continuously monitor systems for unusual behavior and review logs to detect potential security incidents early.
Following guidelines from organizations like the National Institute of Standards and Technology can help ensure your cybersecurity strategy is aligned with industry best practices.
Implementing these cybersecurity practices creates a strong defense against modern cyber threats and helps maintain a safe and secure digital environment.
Cybersecurity Tools and Technologies
Cybersecurity relies on a wide range of tools and technologies designed to detect, prevent, and respond to cyber threats. These solutions work together to create a multi-layered defense system for protecting data, networks, and devices.
Firewalls
Firewalls act as the first line of defense by monitoring incoming and outgoing network traffic. They block unauthorized access while allowing legitimate communication.
Antivirus and Anti-Malware Software
Security software like Microsoft Defender Antivirus helps detect, quarantine, and remove malicious programs such as viruses, spyware, and ransomware.
Intrusion Detection and Prevention Systems (IDPS)
These systems monitor network activity for suspicious behavior and can automatically take action to stop potential threats before they cause damage.
Encryption Technologies
Encryption protects sensitive data by converting it into unreadable code. Only authorized users with the correct decryption key can access the information.
Security Information and Event Management (SIEM)
SIEM tools collect and analyze security data from multiple sources in real time, helping organizations detect and respond to incidents quickly.
Endpoint Detection and Response (EDR)
EDR solutions monitor devices such as laptops and servers to identify threats and respond to suspicious activities at the endpoint level.
Identity and Access Management (IAM)
IAM systems control who can access resources within an organization. They enforce authentication methods such as multi-factor authentication (MFA).
Vulnerability Scanners
These tools scan systems for known weaknesses and provide recommendations to fix them before attackers can exploit them.
Penetration Testing Tools
Pen testing tools simulate cyberattacks to identify security gaps. Ethical hackers use them to strengthen defenses proactively.
Many cybersecurity frameworks and best practices are guided by organizations like the National Institute of Standards and Technology, which provide structured approaches to managing and reducing cyber risks.
By combining these tools and technologies, individuals and organizations can build a strong cybersecurity posture and effectively defend against evolving threats.
Real-World Cybersecurity Incident
A well-known example of a major cyberattack is the WannaCry ransomware attack. This incident occurred in May 2017 and rapidly spread across more than 150 countries, infecting hundreds of thousands of computers.
WannaCry exploited a vulnerability in older versions of Microsoft Windows, particularly systems that had not installed recent security updates. Once infected, the ransomware encrypted files and demanded payment in cryptocurrency to restore access.
Major organizations, including hospitals, banks, and government agencies, were severely impacted. For example, parts of the National Health Service in the United Kingdom experienced widespread disruption, forcing cancellations of appointments and critical services.
This incident highlighted several key lessons:
- The importance of keeping systems updated
- The risks of outdated software
- The need for strong backup and recovery strategies
- The global impact of cyber threats
The WannaCry attack remains a powerful reminder that even a single vulnerability can lead to widespread damage if not addressed promptly.
Benefits of Strong Cybersecurity
Strong cybersecurity is essential for protecting digital assets and maintaining trust in today’s connected world. Whether for individuals or organizations, implementing effective security measures provides several key advantages.
Protection Against Data Breaches
Robust cybersecurity helps prevent unauthorized access to sensitive information such as personal data, financial records, and business secrets.
Reduced Financial Loss
Cyberattacks can lead to significant financial damage. Strong security minimizes the risk of fraud, ransomware payments, and recovery costs.
Enhanced Privacy
Cybersecurity ensures that personal and confidential data remains private and protected from cybercriminals.
Improved Business Continuity
By preventing disruptions caused by attacks, organizations can maintain smooth operations and avoid downtime.
Increased Customer Trust
Companies that prioritize cybersecurity build stronger relationships with customers by demonstrating a commitment to data protection.
Compliance With Regulations
Following cybersecurity best practices helps organizations meet standards set by bodies like the International Organization for Standardization, reducing legal risks.
Protection Against Emerging Threats
Advanced security tools can detect and respond to new and evolving cyber threats in real time.
Better System Performance
Well-secured systems are less likely to be compromised, resulting in more stable and reliable performance.
Strong cybersecurity is not just about defense—it is a strategic investment that supports long-term growth, trust, and digital safety.
Future Trends in Cybersecurity
Cybersecurity is rapidly evolving to keep pace with increasingly sophisticated cyber threats. As digital transformation accelerates, new technologies and strategies are shaping the future of how data and systems are protected.
Artificial Intelligence and Machine Learning
AI and machine learning are transforming cybersecurity by enabling faster threat detection and automated responses. These technologies can analyze vast amounts of data to identify unusual patterns and prevent attacks before they occur.
Zero Trust Security Model
The Zero Trust approach assumes that no user or device should be trusted by default, even inside a network. This model enforces strict verification for every access request, reducing the risk of internal and external threats.
Cloud Security Advancements
As more organizations move to cloud platforms, securing cloud environments becomes critical. Advanced encryption, identity management, and monitoring tools help protect data stored in the cloud.
Internet of Things (IoT) Security
With billions of connected devices, IoT security is a growing concern. Future cybersecurity strategies will focus on securing smart devices, from home appliances to industrial systems.
Automation and Security Orchestration
Automation tools are helping organizations respond to threats more efficiently. Security orchestration platforms streamline processes, reducing response time and human error.
Regulatory Compliance and Standards
Global standards from organizations like the International Organization for Standardization will continue to shape cybersecurity practices, ensuring consistency and accountability.
Quantum Computing Impact
Quantum computing has the potential to break traditional encryption methods. Researchers are developing quantum-resistant algorithms to prepare for this future risk.
Human-Centric Security
As human error remains a major vulnerability, future cybersecurity efforts will focus more on user education, awareness training, and behavior analysis.
Cybersecurity will continue to evolve alongside technology. Staying informed about these trends helps individuals and organizations prepare for future challenges and build stronger digital defenses.
Frequently Asked Questions (FAQ)
What is cybersecurity?
Cybersecurity is the practice of protecting systems, networks, and data from cyber threats and unauthorized access.
Why is cybersecurity important?
It prevents data breaches, protects sensitive information, and ensures safe digital operations.
What are the main types of cyber threats?
Common threats include malware, phishing, ransomware, and denial-of-service attacks.
How can I improve cybersecurity?
Use strong passwords, enable multi-factor authentication, update systems, and use trusted security tools.
What tools are used in cybersecurity?
Common tools include firewalls, antivirus software, encryption, and monitoring systems.
Conclusion
Cybersecurity is a fundamental part of modern digital life. As technology continues to evolve, so do the risks associated with cyber threats. From protecting personal data to ensuring business continuity, strong cybersecurity practices are essential for staying safe online.
By understanding key concepts, recognizing common threats, and using reliable tools like Microsoft Defender Antivirus, individuals and organizations can significantly reduce their risk of attacks.
Following established guidelines from organizations such as the National Institute of Standards and Technology also helps build a structured and effective security strategy.
In the end, cybersecurity is not just about technology—it is about awareness, prevention, and continuous improvement. Taking proactive steps today can help protect your digital future.