Network security is the practice of protecting computer networks from unauthorized access, misuse, and cyberattacks. It involves a combination of hardware, software, and policies designed to ensure the safety of data as it travels across networks.
Network security applies to both small home networks and large enterprise infrastructures.
Why Network Security Is Important
Network security is essential for protecting data, systems, and communication across digital networks. As cyber threats become more advanced, securing networks is critical for both individuals and organizations.
Protects Sensitive Data
Network security ensures that confidential information—such as personal details, financial records, and business data—remains safe from unauthorized access.
Prevents Unauthorized Access
Strong security measures block hackers and malicious users from gaining entry to networks and connected systems.
Reduces Risk of Cyberattacks
Effective network protection helps defend against threats like malware, phishing, and Distributed Denial-of-Service (DDoS) attacks.
Ensures Business Continuity
Cyberattacks can disrupt operations and cause downtime. Network security helps maintain stable and uninterrupted services.
Safeguards User Privacy
By securing data transmission, network security protects users from data leaks and unauthorized surveillance.
Supports Compliance Requirements
Organizations must follow security standards set by bodies like the National Institute of Standards and Technology to meet legal and regulatory requirements.
Builds Trust and Reputation
A secure network increases confidence among customers and users, strengthening trust and credibility.
Network security is not just a technical necessity—it is a vital component of protecting digital environments and ensuring safe, reliable communication in today’s connected world.
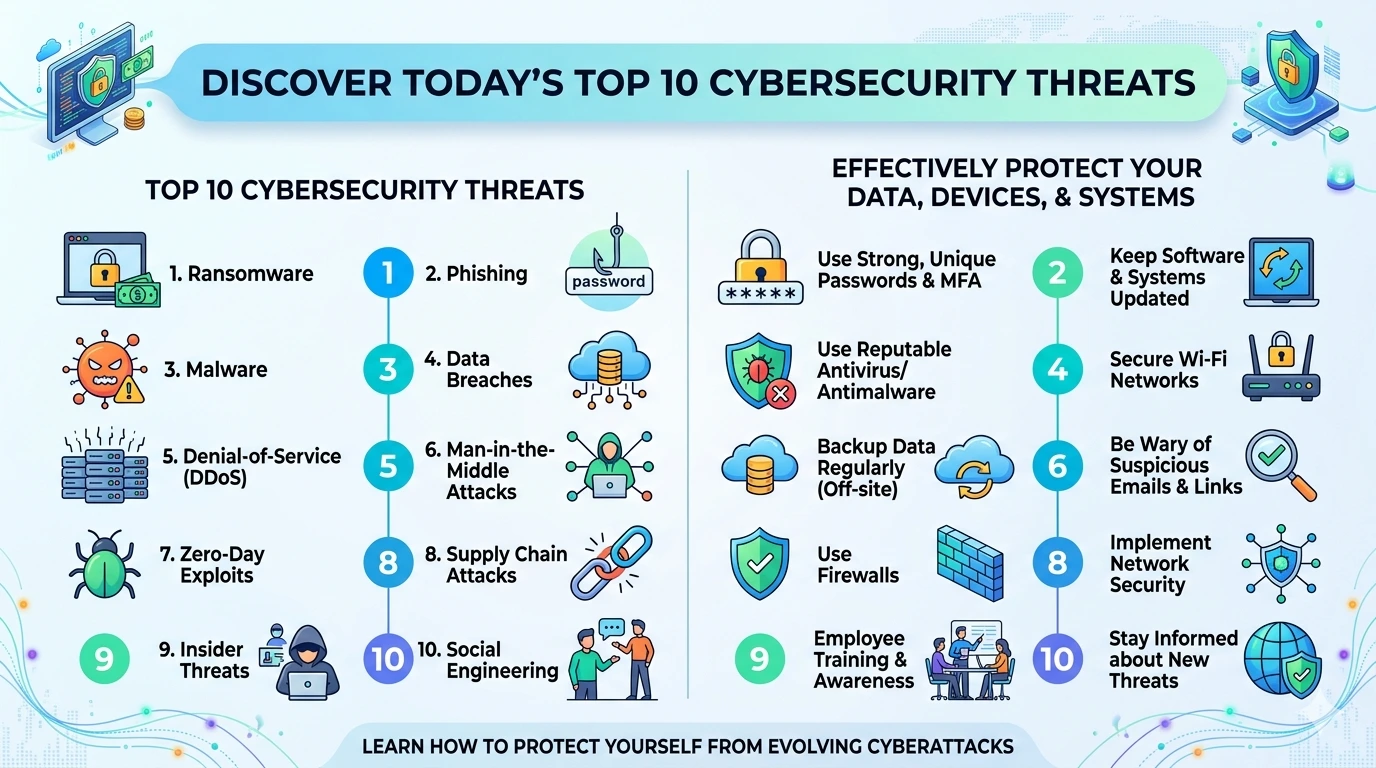
Common Network Security Threats
Network security threats are constantly evolving, targeting systems, data, and communication channels. Understanding these threats is essential for building strong defenses and protecting your network from potential attacks.
Malware
Malware is malicious software that can spread across networks and infect connected devices. It can steal data, damage systems, or give attackers control over network resources.
Phishing Attacks
Phishing tricks users into revealing login credentials or sensitive information, which attackers can use to gain unauthorized access to networks.
Distributed Denial-of-Service (DDoS) Attacks
DDoS attacks flood networks or servers with excessive traffic, causing services to slow down, crash, or become unavailable.
Man-in-the-Middle (MitM) Attacks
In MitM attacks, cybercriminals intercept communication between users and systems, allowing them to steal or manipulate transmitted data.
Unauthorized Access
Weak passwords, misconfigured systems, or unpatched vulnerabilities can allow attackers to gain unauthorized access to networks.
Insider Threats
Employees or authorized users may intentionally or accidentally expose sensitive data, creating security risks within the network.
Zero-Day Exploits
These attacks target unknown vulnerabilities in software or network systems before developers release fixes, making them difficult to defend against.
DNS Spoofing
Attackers manipulate Domain Name System (DNS) records to redirect users to malicious websites without their knowledge.
Password Attacks
Techniques such as brute force or credential stuffing are used to guess or reuse passwords to gain access to network systems.
Botnet Attacks
A botnet is a network of infected devices controlled by attackers to launch large-scale attacks such as DDoS or spam campaigns.
Many organizations follow security frameworks from the National Institute of Standards and Technology to identify and mitigate these threats effectively.
By understanding these common network security threats, you can take proactive steps to strengthen your defenses and protect your systems from potential cyberattacks.
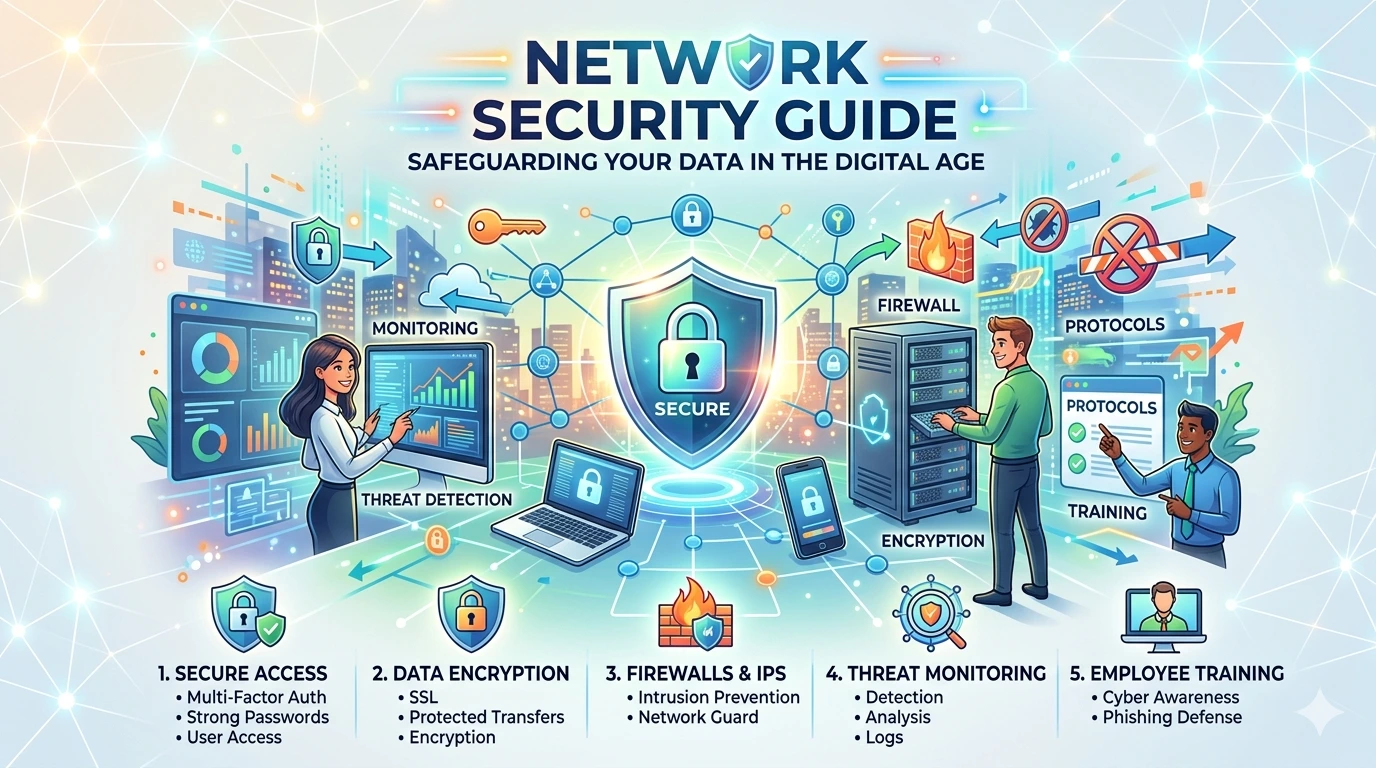
Best Practices for Network Security
Implementing strong network security practices is essential to protect systems, data, and communication from cyber threats. By following these best practices, individuals and organizations can significantly reduce vulnerabilities and improve overall security.
Use Strong Passwords and Authentication
Create complex, unique passwords for all network devices and accounts. Enable multi-factor authentication (MFA) to add an extra layer of protection.
Keep Systems and Firmware Updated
Regularly update operating systems, routers, and network devices to patch known vulnerabilities. Stay current with updates via the Microsoft Security Update Guide.
Enable Network Encryption
Use strong encryption protocols such as WPA3 for Wi-Fi networks to protect data transmitted over the network.
Install Firewalls and Security Software
Firewalls monitor and control traffic, while tools like Microsoft Defender Antivirus help detect and block threats on connected devices.
Segment Your Network
Divide your network into smaller segments to limit the spread of attacks and improve control over sensitive areas.
Monitor Network Traffic
Continuously monitor activity to detect unusual behavior or potential intrusions early.
Limit Access and Permissions
Only allow authorized users and devices to access your network. Apply the principle of least privilege to reduce risk.
Secure Wireless Networks
Change default router settings, disable unused features, and hide SSIDs if necessary to reduce exposure.
Use Virtual Private Networks (VPNs)
VPNs encrypt internet connections, especially when accessing networks remotely or using public Wi-Fi.
Conduct Regular Security Audits
Perform periodic assessments to identify vulnerabilities and ensure security measures are effective.
Following guidelines from organizations like the National Institute of Standards and Technology helps ensure your network security strategy aligns with industry standards.
Adopting these best practices creates a strong defense against cyber threats and ensures a safer, more reliable network environment.
Types of Network Security
Network security includes multiple layers of protection designed to safeguard systems, data, and communication across networks. Each type focuses on a specific aspect of security to create a comprehensive defense strategy.
Firewall Security
Firewalls act as a barrier between trusted and untrusted networks. They monitor and control incoming and outgoing traffic based on predefined security rules.
Intrusion Detection and Prevention Systems (IDPS)
IDPS tools monitor network traffic for suspicious activity and can automatically block potential threats before they cause damage.
Virtual Private Networks (VPNs)
VPNs encrypt internet connections, ensuring secure communication—especially when accessing networks remotely or using public Wi-Fi.
Network Access Control (NAC)
NAC systems regulate who and what devices can access a network, ensuring only authorized users and compliant devices are allowed entry.
Wireless Security
Wireless security focuses on protecting Wi-Fi networks using encryption protocols like WPA2 or WPA3, along with secure configurations.
Application Security
Application security ensures that software running on the network is protected from vulnerabilities and exploits.
Endpoint Security
Endpoint security protects devices such as computers and smartphones connected to the network using tools like Microsoft Defender Antivirus.
Data Loss Prevention (DLP)
DLP solutions prevent sensitive data from being leaked, shared, or accessed without authorization.
Cloud Network Security
This type focuses on protecting cloud-based infrastructure, applications, and data using advanced security controls and monitoring tools.
Email Security
Email security systems filter out spam, phishing attempts, and malicious attachments to protect users and networks.
Many organizations implement these types of network security following standards from the International Organization for Standardization to ensure consistent and effective protection.
By combining these different types of network security, organizations can build a layered defense system that reduces vulnerabilities and protects against a wide range of cyber threats.
Benefits of Strong Network Security
Strong network security provides essential protection for systems, data, and communication. It helps individuals and organizations maintain safe, reliable, and efficient digital environments.
Protects Sensitive Data
Network security safeguards confidential information such as personal data, financial records, and business assets from unauthorized access and breaches.
Prevents Cyberattacks
Effective security measures reduce the risk of attacks like malware, phishing, and Distributed Denial-of-Service (DDoS), keeping systems secure.
Ensures Business Continuity
By preventing disruptions and downtime, network security helps organizations maintain smooth and uninterrupted operations.
Enhances User Privacy
Secure networks protect users from data leaks, surveillance, and unauthorized tracking.
Improves System Performance
Well-secured networks are less likely to be compromised, resulting in more stable and efficient performance.
Builds Trust and Reputation
Organizations that prioritize security gain customer confidence and strengthen their reputation.
Supports Regulatory Compliance
Following security standards from organizations like the National Institute of Standards and Technology helps meet legal and industry requirements.
Reduces Financial Risks
Preventing cyber incidents helps avoid costs related to data breaches, recovery, and potential legal penalties.
Enables Secure Remote Access
With tools like VPNs and encryption, users can safely access networks from remote locations.
Protects Against Emerging Threats
Strong network security systems can detect and respond to new and evolving cyber threats in real time.
Implementing strong network security is a strategic investment that ensures long-term protection, reliability, and trust in an increasingly connected world.
Future Trends in Network Security
Network security is rapidly evolving as organizations face more complex and sophisticated cyber threats. Emerging technologies, changing infrastructures, and new attack methods are shaping the future of how networks are protected.
Artificial Intelligence (AI)-Driven Security
AI is transforming network security by enabling predictive threat detection and automated responses. Modern systems can analyze behavior, detect anomalies, and respond to threats in real time—sometimes without human intervention. (INE)
Zero Trust Architecture
The traditional “trust but verify” model is being replaced by Zero Trust, where no user or device is trusted by default. Every access request is continuously verified, reducing the risk of unauthorized access.
Identity-Centric Security
Identity is becoming the new security perimeter. Instead of focusing only on networks, organizations are prioritizing identity protection, including user credentials and machine identities. (Forbes)
Cloud and Hybrid Security Expansion
As businesses adopt cloud and hybrid environments, network security must adapt. Securing multi-cloud systems and managing complex infrastructures are becoming top priorities. (INE)
Secure Access Service Edge (SASE)
SASE combines networking and security into a unified cloud-based service. It provides secure access regardless of user location, making it ideal for remote work and distributed networks. (TechRadar)
Post-Quantum Cryptography
With the rise of quantum computing, traditional encryption methods may become vulnerable. Organizations are preparing by developing quantum-resistant encryption technologies. (Nomios Group)
Automation and Orchestration
Security automation is helping organizations respond faster to threats. Automated systems can detect, analyze, and mitigate attacks with minimal human intervention, improving efficiency and response time. (INE)
Expanding Attack Surface Management
As digital infrastructures grow, so does the number of potential entry points for attackers. Managing and securing this expanding attack surface is becoming a critical focus. (INE)
AI-Powered Cyber Threats
While AI strengthens defenses, attackers are also using it to launch more advanced attacks, including automated phishing and vulnerability exploitation. (World Economic Forum)
Regulatory and Compliance Pressure
Governments and organizations are introducing stricter cybersecurity regulations. Companies must adopt stronger security measures to meet compliance requirements and avoid penalties. (INE)
The future of network security is driven by speed, automation, and intelligence. As threats become more advanced, organizations must adopt modern security models, leverage AI, and focus on identity and cloud protection.
Staying ahead of these trends is essential to building resilient and secure network infrastructures in an increasingly digital world.
Frequently Asked Questions (FAQ)
What is network security?
Network security is the process of protecting networks, systems, and data from unauthorized access and cyber threats.
Why is network security important?
It prevents data breaches, protects sensitive information, and ensures systems remain operational.
What are examples of network security tools?
Firewalls, VPNs, antivirus software, and intrusion detection systems are common tools.
How can I improve network security?
Use strong passwords, enable encryption, update systems, and monitor network activity.
What is the biggest network security threat?
DDoS attacks, phishing, and malware are among the most common threats today.
Conclusion
Network security is a critical part of modern cybersecurity. As threats continue to evolve, implementing strong security measures is essential to protect systems, data, and users.
By following best practices and using reliable tools, individuals and organizations can build a secure network environment and reduce the risk of cyberattacks.